Advanced Threat Hunting Harnessing Chronicle Backstory with Demisto
Simplifying Threat Hunting & Remediation by harnessing Chronicle Backstory capabilities with Demisto’s Intelligence orchestration.
The cybersecurity landscape is changing rapidly with the advent of technology. With the introduction of mobiles, BYOD devices, wireless, etc. the attack surface has risen multifold. This coupled with the advanced nature of threats, which makes them stealthier day by day, the Security Operations team is up for an uphill task.
Traditionally, the cybersecurity has been about securing the core enterprise by fortifying the perimeter. However, this defensive approach is not sufficient when a threat gets into the enterprise. One of the studies reveals that an average dwell time for a threat has been in the range of 400 days. This not only fatigues the SOC team but damages the reputation of the organization.
With the changing threat landscape, the cybersecurity approach needed a tectonic shift. Hackers and attackers evolve to find ways to get into the impenetrable security wall.
The cybersecurity approach was required to be more offensive given the nature of advanced threats. Rather than reacting to the adversary, one should proactively prevent it at the source. Threat hunting is the pro-active approach in cybersecurity that most of the SOC employ nowadays.
Google Cloud’s Chronicle Backstory wanted to integrate its powerful cybersecurity platform with Demisto’s SOAR capabilities and harness the orchestration capabilities with context-rich telemetry data.
Chronicle Backstory is a global cloud service where companies can privately upload, store, and analyze their internal security telemetry to detect and investigate potential cyber threats. Backstory provides powerful threat hunting capabilities by correlating scale security telemetry data with threat intelligence context. The platform build on top of Google Cloud infrastructure allows you to upload security telemetry, including high-volume data such as DNS traffic, Netflow, endpoint logs, proxy logs, etc. so that it can be indexed and automatically analyzed by the analytics engine.
Demisto (now part of Palo Alto Networks) is a platform that provides SOAR (Security Orchestration, Automation and Response) solutions targeted towards security operations centers. The SOAR technology market aims to converge security orchestration and automation (SOA), security incident response (SIR) and threat intelligence platform (TIP) capabilities into single solutions. Demisto aims at unifying the people, processes, and technology for the Security Operations Center.
Crest helped Chronicle Backstory build the Demisto integration, which allows Backstory’s correlated telemetry to be tied with Demisto and assist SOC analyst to remediate and prevent advanced threats. Crest has integrated most of the Backstory’s capabilities available via Search APIs with Demisto.
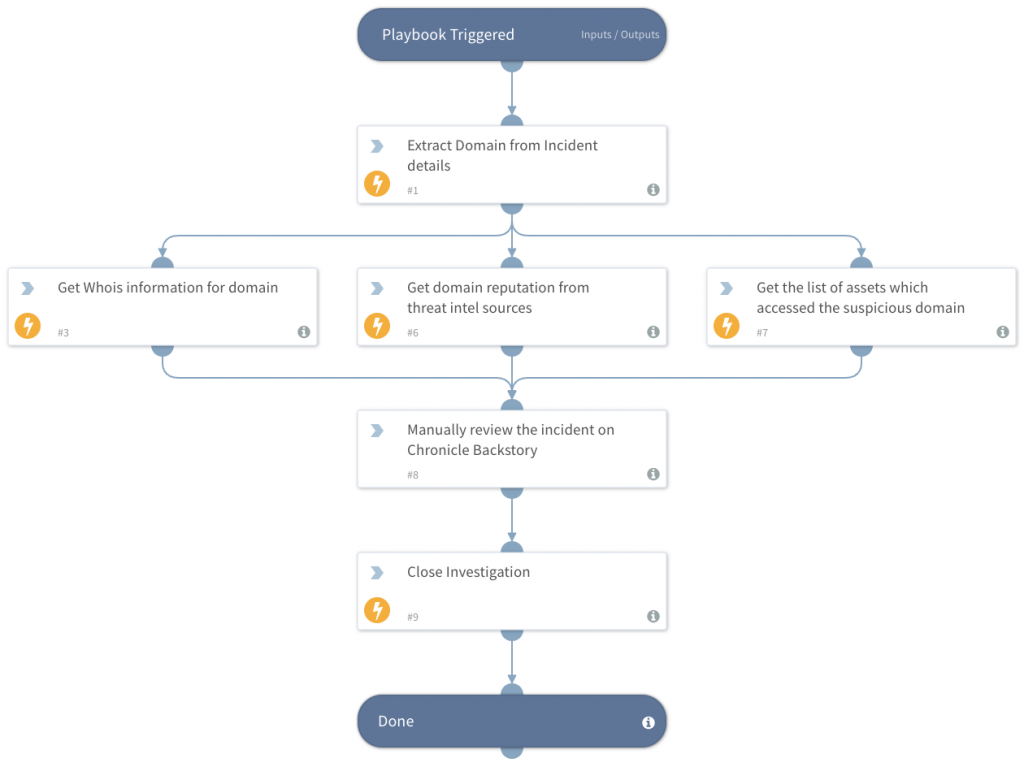
Engaging the Chronicle Backstory integration in Demisto, SOC can channel the IOC Domain matches reported to Backstory as actionable intelligence. IOC Domain matches are suspicious domains observed in an enterprise recently. Backstory relies on various threat intel platforms to correlate an enterprise’s security telemetry with valuable intelligence context. As part of the investigation, the SOC analyst would like to get the details of assets within the enterprise that accessed the suspicious domain and understand the spread of the suspicious activity. This can be done by a simple command execution on Demisto w/o hopping over multiple platforms. The integration also empowers the SOC analyst with valuable threat intel context from Backstory seamlessly. Refer to the sample threat hunting and remediation playbook.

AUTHOR –
SHIVANG PATEL
Shivang leads the Security Analytics and Automation team at Crest Data Systems. Shivang brings 12+ years of experience in the area of Security software development and Security operations for large enterprises. Over the past 5 years a Crest, he has led several projects to help build 100+ integrations in the security ecosystem. Prior to Crest, Shivang was working with Wipro Technologies in the telecom vertical. Shivang holds Bachelor of Engineering with specialization in Electronics and communications from ADIT, Sardar Patel University.