Best of Both Worlds – Deep SIEM Insights with Powerful Business Intelligence Dashboards: Google Chronicle + Looker

Introduction to SIEM
Security information and event management (SIEM) solutions collect a range of security and other data from security controls and devices throughout the IT environment.
In the early days, it used to be focused on log management, but modern SIEM solutions help you correlate malware findings with context, user and application data, threat intelligence, and organizational information.
SIEM solution architectures provide advanced analytical tools and workflows to quickly inspect very large data sets, identify attacks, and help devise corrective actions.
In order to interrogate and identify the attacks, there is a need for a system that can store and process the enterprise security telemetry and a Business Intelligence tool that visualizes the data collected to derive the statistics. The former could be sufficed by Google’s SIEM solution Chronicle and the latter by a BI tool Looker which is now a part of Google Cloud.
About Chronicle
Chronicle is a global security telemetry platform for investigating incidents and hunting for threats in your enterprise network. Purpose-built on core Google infrastructure, the Chronicle can ingest massive amounts of telemetry data, normalize it, index it, correlate it to known threats, and make it available for analysis in seconds.
About Looker
Looker is a cloud-based business intelligence (BI) platform designed to explore and analyse data. It is a business intelligence software and big data analytics platform that helps you explore, analyse, and share real-time business analytics easily. It helps businesses to capture and analyse data from multiple sources and make data-driven decisions.
Business Intelligence solution having Chronicle + Looker
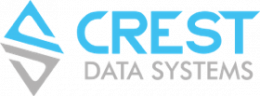
A Solution Architecture having both of these i.e. Chronicle + Looker in the technology stack can generate very meaningful and useful insights such as Events over time, Global Threat Matches, Top N Rule Alerts by severity or rule matches, Top N Domains, IP Traffic Analysis, Authentication activity and many more.

Varied Log Forwarders can forward the logs and telemetry such as security logs event data, IOC data, Rule detections, and other Ingestion metrics to the Chronicle platform. This in turn can then be analysed within Chronicle with the help of ML techniques wherever applicable and be exported to data warehouse solutions such as BigQuery based on customer need. The exported data can then be visualized in BI tools like Looker to enable the SOC analysts and Admins to get business and security insights out of this data.
Example:
Parent Dashboard showing the overall statistics of Event count, throughput in GBs and Alert counts along with the delta difference of the previous period: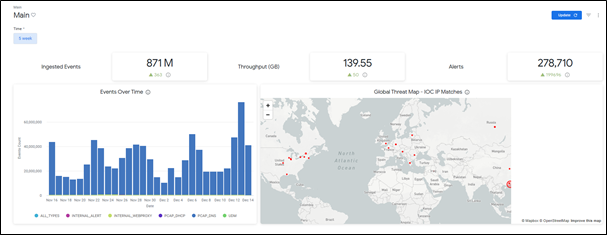

The Crest Difference
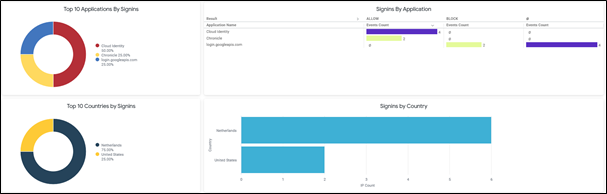
Crest Data Systems helped Chronicle to create dashboards in Looker for threat summary and export as Looker Blocks in Looker Marketplace.
Business Goal was to create enhanced insights with the Looker visualizations having features such as Threat Geo maps, data trendlines, the period over period analysis, etc. which shall display integrated and correlated views of UDM events, Rule matches, Ingestion metrics information, and IOC Matches with several drill-downs till asset, user, IP addresses, domain and many more.
Advantages of using Google Chronicle Looker Block
- Valuable insights in less time
- Self-service reporting for Chronicle with merged dataset views
- Capability of creation of custom dashboards by SOC Analysts and admins

AUTHOR: –
DIPIKA MANSUKHANI
Dipika Mansukhani is working as a Senior Technical Lead at Crest Data Systems. She has 14+ years of experience in the areas of Big Data technologies like Hadoop; NoSQL databases like MongoDB, HBASE; Analytics solutions like ELK; Java, Python, Web Services, etc. Before joining Crest, Dipika worked as a Solutions Lead for Big Data solutions in her previous company and also as a Team Lead for project delivery. She holds a Masters Degree in Computer Applications from GLS University.